Verify the protocol contract address
Before you connect your wallet or approve any transactions, you must confirm you are interacting with the official Base DeFi protocol. Phishing sites often mimic legitimate interfaces, directing users to fake contracts that drain funds. A single typo or a copied link from an untrusted source can lead to a irreversible loss of capital.
Always start at the official Base ecosystem page to find verified links. Do not rely on search engine ads or social media comments, which are common vectors for scams. Cross-reference the contract address found on the official site with a block explorer like Etherscan or Basescan. Look for the "Verified" badge and check the creator's identity to ensure the code matches the published source.
Check total value locked and volume
Total value locked (TVL) and trading volume are the primary indicators of a protocol’s health and liquidity depth. High TVL suggests that significant capital is committed to the platform, while consistent volume confirms that assets can be bought and sold without severe price slippage. Together, they act as a buffer against market volatility and reduce the risk of encountering illiquid pools where exits are impossible.
When evaluating Base DeFi protocols, use DeFiLlama to review the chain’s aggregate metrics and individual protocol rankings. A protocol with a shrinking TVL or declining daily volume may be losing user trust or facing technical issues. Look for stable or growing trends rather than sudden spikes, which can sometimes indicate temporary incentives rather than sustainable demand.
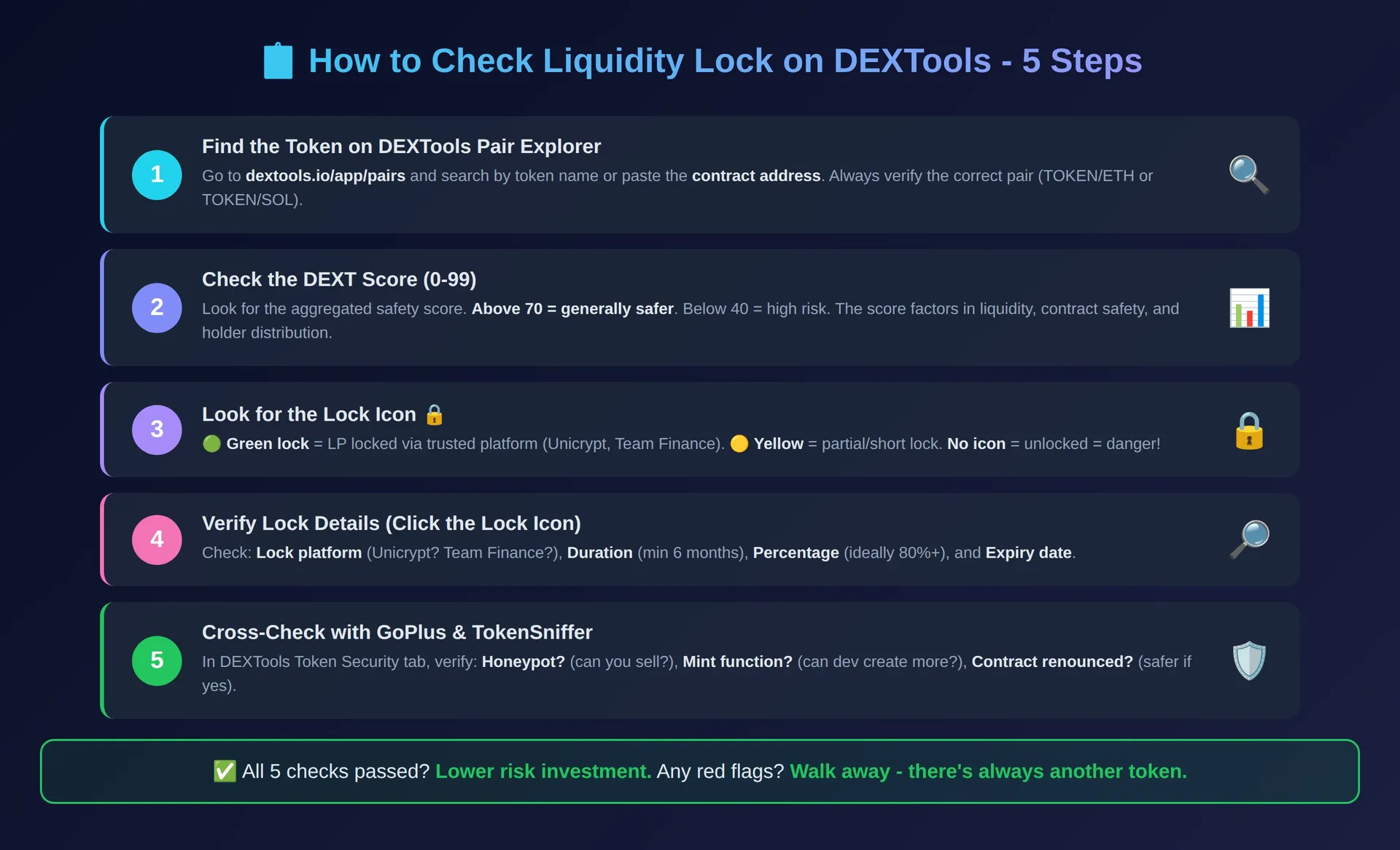
Avoid protocols with low liquidity relative to their market cap. Thin liquidity pools are vulnerable to "rug pulls" or large sell-offs that can crash prices instantly. Prioritize platforms with deep order books and high trading activity, as these provide the stability needed for long-term liquidity provision.
Review audit reports and bug bounties
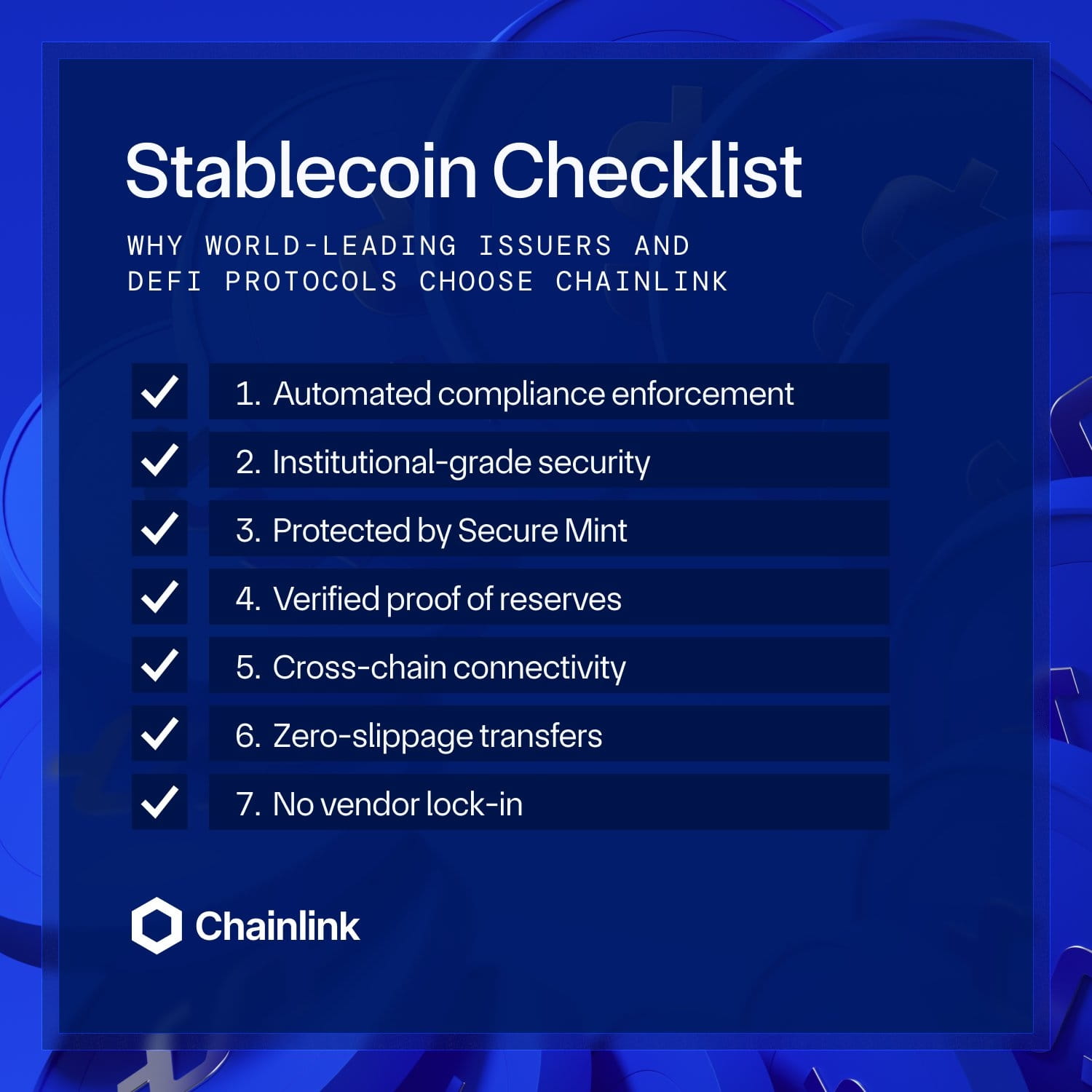
Before depositing funds into a Base DeFi protocol, verify that its smart contracts have undergone professional security audits. Audits are independent reviews by specialized firms that scan code for vulnerabilities, logic errors, and potential exploit vectors. A clean audit report is your primary shield against technical failures, though it is not an absolute guarantee of safety.
Look for audits conducted by reputable firms with established track records in the DeFi space. Check the project’s documentation for links to these reports, typically hosted on the firm’s website or a dedicated security dashboard. Pay attention to the severity of any identified issues; critical bugs must be resolved before mainnet deployment. If a protocol launched without an audit, treat it as a high-risk experiment rather than a standard investment vehicle.
In addition to audits, check if the protocol participates in a bug bounty program. These programs incentivize white-hat hackers to find and report vulnerabilities in exchange for rewards. Platforms like Immunefi host many of these bounties, offering transparency into a protocol’s security posture. A substantial bounty indicates that the team is actively monitoring for threats and values community-driven security.
Start with small test transactions
Before committing significant capital to a Base DeFi liquidity pool, treat your first deposit as a controlled experiment. This step isolates technical friction from market risk, ensuring you understand the specific withdrawal mechanics of the protocol you are using.
1. Deposit a minimal amount
Transfer a small, manageable amount of assets (e.g., $10-$50 worth) into the liquidity pool. This amount is large enough to trigger the smart contract interactions but small enough to absorb potential slippage or gas inefficiencies without impacting your overall financial position.
2. Verify the position
Check your wallet and the protocol dashboard to confirm the liquidity position is recorded correctly. Ensure the token pair and ratio match your expectations. If the position does not appear immediately, check the Base network block explorer for the transaction receipt.
3. Execute a full withdrawal cycle
Remove your liquidity and withdraw the assets back to your wallet. This is the most critical test. Many DeFi protocols have complex withdrawal windows, lock-up periods, or specific claim mechanisms that differ from standard swaps. A successful withdrawal confirms you can access your funds.
4. Review gas and timing
Note the time it took for the transaction to confirm and the gas fees paid. Compare this to the network's average. If the withdrawal is unusually slow or expensive, investigate whether the pool has low liquidity or if the contract has known inefficiencies.
5. Confirm asset integrity
Once the withdrawal is complete, verify that the assets returned to your wallet match the expected value, accounting for any trading fees or impermanent loss incurred during the test period. If the numbers align, you have validated the protocol's operational reliability.
This "dry run" approach prevents the common scenario where a user locks up significant capital only to find that withdrawing it requires a multi-day waiting period or complex multi-step process. By testing with small amounts, you build confidence in the Base DeFi wallet interface and the specific smart contract you are interacting with.
Understand impermanent loss risks
Use this section to make the Base DeFi Safety Checklist for New Liquidity Providers decision easier to compare in real life, not just on paper. Start with the reader's actual constraint, then separate must-have requirements from details that are merely nice to have. A practical choice should survive normal use, maintenance, timing, and budget. If a recommendation only works in an ideal situation, call that out plainly and give the reader a fallback path.
The simplest way to use this section is to write down the must-have criteria first, then compare each option against those criteria before weighing nice-to-have features.


No comments yet. Be the first to share your thoughts!